Last Updated on December 26, 2022 by Mat Diekhake
In older versions of Windows—like Windows 7, Windows Vista and Windows XP—before Windows 10 came out, the Windows operating system would pop up a message on the computer’s screen if you did not have any antivirus installed and tell you to install some. Windows did not provide any antivirus for you, so you then needed to work out which antivirus you wanted to install from a third-party. So you would then hunt around the internet and try to find a good mix between antivirus that was getting good reviews and antivirus that was available at a good price; it was a huge pain in the butt.
Microsoft then finally came to its senses and started developing an antivirus solution of their own—that antivirus was named Windows Defender. The Windows Defender used to be available as part of the Microsoft Security Essentials, so it is not like Windows Defender is entirely new, but it is much better than it used to be.
Some people still wonder whether Windows Defender is good enough to be the antivirus of choice to have installed on a computer, even with it’s much better capabilities than years ago. That is not an easy question to answer—even for tech enthusiasts who write about tech for a living. I’m sure many people would disagree with each other’s opinions if you were to ask a bunch of different writers from various sites.
From our experience, we say yes: Windows Defender is good enough to keep installed on your operating system and used as your only antivirus solution. For starters, scanning with Windows Defender is really easy to do. We have covered a full how-to guide already that covers how to use Windows Defender in detail. That same guide also shows you how you can easily scan individual files as you roam freely around the Windows 10 operating system. For example, if you open File Explorer, you can quickly scan a file in a folder because Microsoft has integrated Windows Defender to be a simple solution when you use Windows—you won’t get that same kind of integration available with other antivirus programs. One of the arguments people make against using Windows Defender is that antivirus isn’t enough to protect a computer anymore and that you need to have a two-in-one antivirus and anti-malware protection working together. Here’s the thing: Windows 10 does have an anti-malware program working in the background also: it is called the Malicious Software Removal Tool. You can find out how to use the Malicious Software Removal Tool if you have not heard about it already.
The following tutorial demonstrates how to turn on and off the Windows Defender antivirus application when you are using aversion of the Windows 10 operating system.
How to Turn On/Off Windows Defender in Windows 10 Using Local Group Policy Editor
You can turn Windows Defender anti-virus on or off using a Group Policy from the Local Group Policy Editor. Here is how to do that:
Note: You’ll need to be using a Windows 10 Pro, Education or Enterprise edition of Windows 10 for this guide to work. You can’t make policy changes in the Local Group Policy Editor using the Windows 10 Home. You can upgrade from Windows 10 Home to Windows 10 Pro by heading to the Settings application if you want to be able to make changes to group policies.
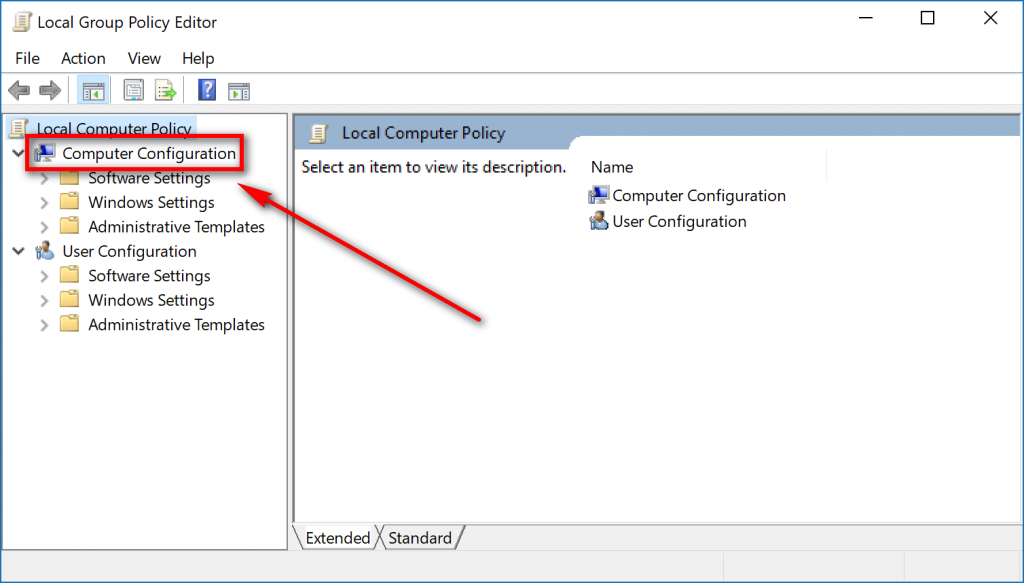
1. To get started, open the Local Group Policy Editor. When it’s open, click on the Computer Configuration in the left side pane.
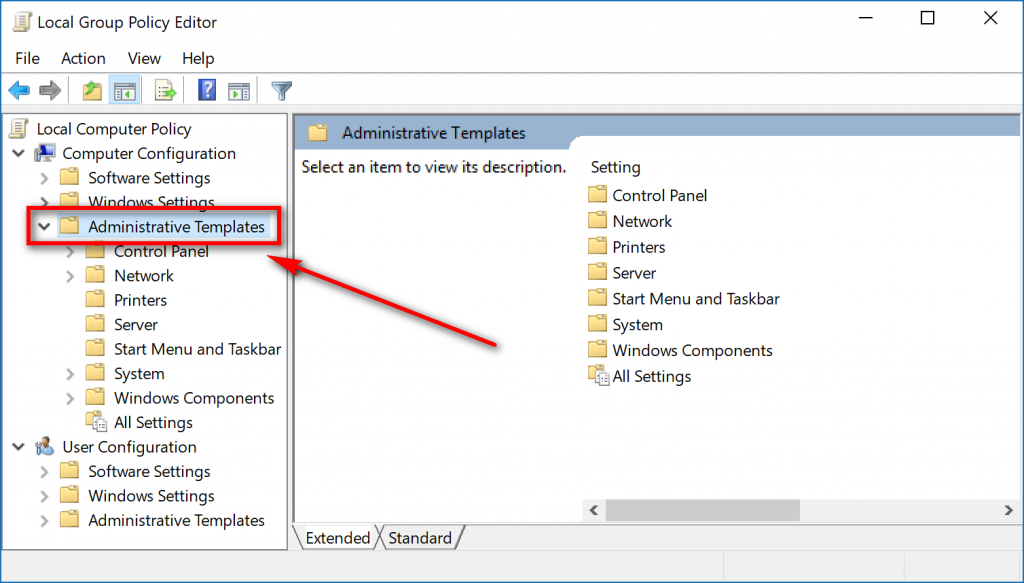
2. Next, click on the Administrative Templates in the left side pane.
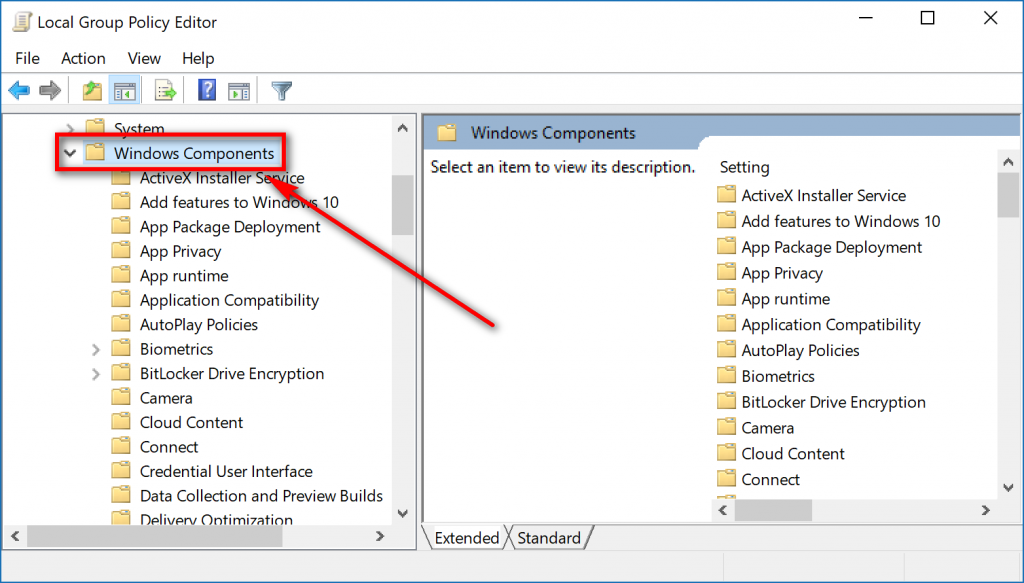
3. Now click on the Windows Components.
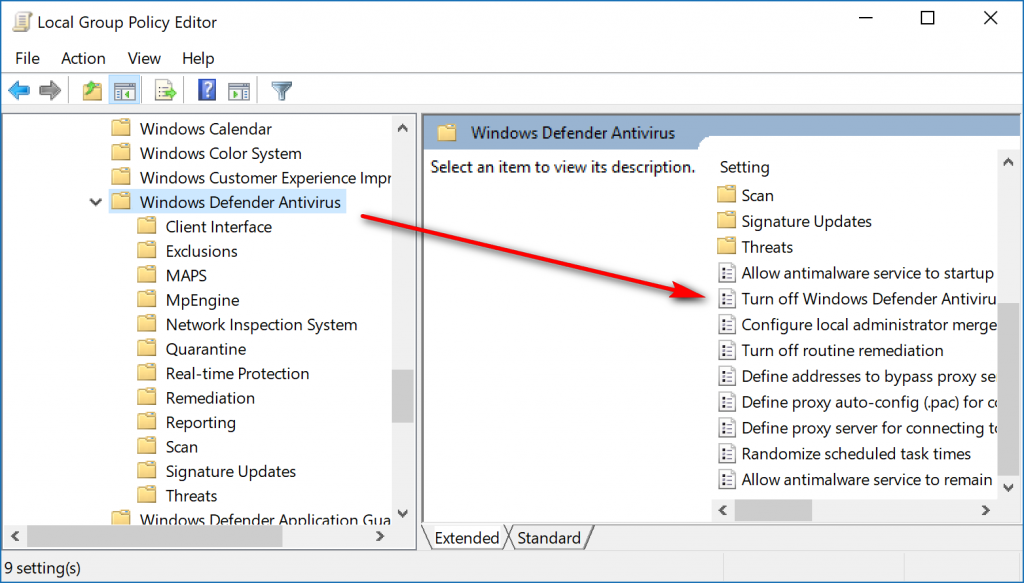
4. Scroll down the list of components until you get to the Windows Defender Antivirus entry and expand it by clicking on it. Now turn your attention to the right side pane and double-click on the Turn off Windows Defender Antivirus entry to bring up the policy window that lets you adjust its settings.
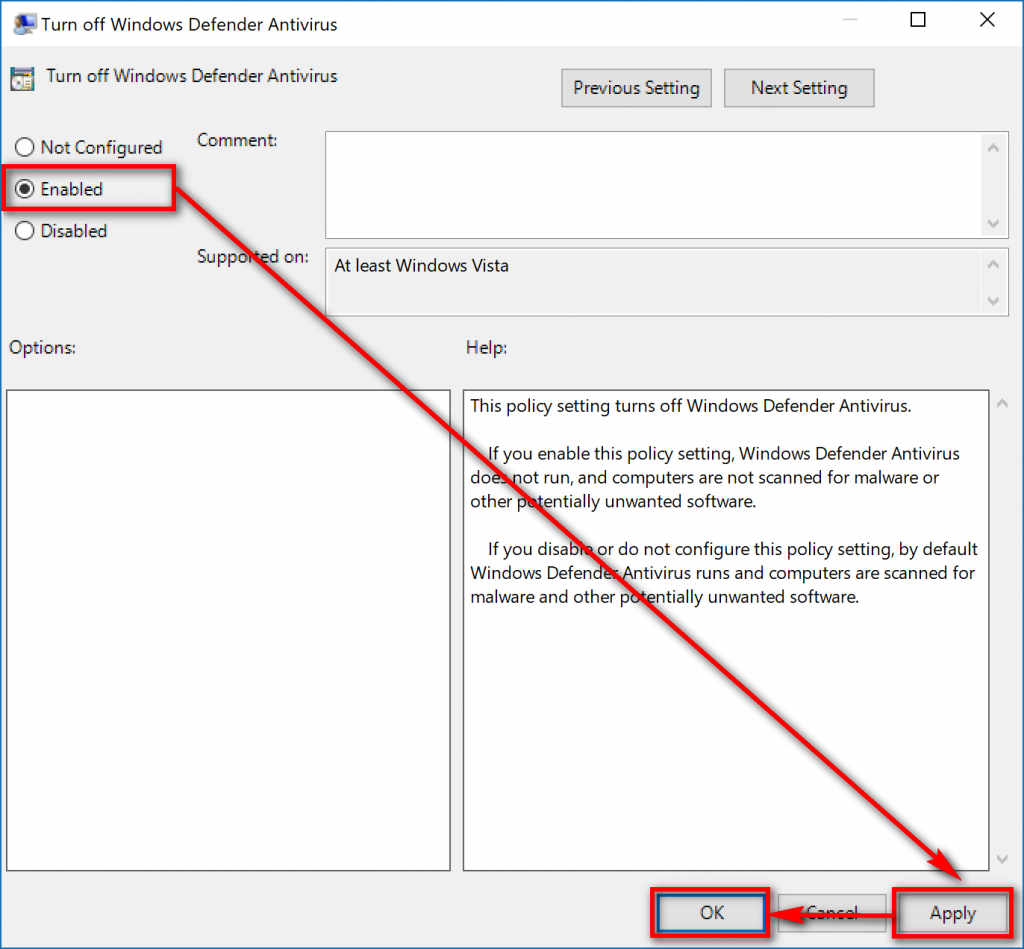
5. By default, the Turn off Windows Defender Antivirus policy is set to Not Configured which means that it won’t be turned off because Windows 10 has it turned on by default. So, to disable it, you need to move the checkmark to the Enable position, click on the Apply > OK buttons down the bottom of the policy window.
Four different types of Group Policies can be applied—administrators only, all users, specific users or groups, or all users except administrators—and the way you do them varies. You’ll still need to be signed in to a user account that has the administrative permissions assigned to it before you can use any of the four options though.
Windows has a Multiple Local Group Policy to help manage computers that are not part of a domain. There are four Local Group Policy Objects (LGPOs) that make up the Multiple Local Group Policy. They are the Local Computer Policy, Administrators Local Group Policy, Non-Administrators Local Group Policy, and a User-Specific Local Group Policy.
All users. The Local Group Policy Editor for all users can be opened by using the Run dialog box, the search field from the taskbar, the Command Prompt and from the PowerShell by using any of the methods available in this guide.
Specific users or groups. The User-Specific LGPO applies user policy settings to specific local users. To do it, you need to press the Windows logo + R keys on your keyboard and then type MMC into the field and clicking on the OK button. Click Yes when prompted by User Account Control. Now in Microsoft Management Console, click on File, followed by Add/Remove snap-in from the menu. Choose the Local Group Policy Editor and click on the Add button. From the Select Group Policy Object window, click on the Browse button. Next, click on the Users tab and then choose the account name from the list, followed by the OK button. You’ll then be directed back to the Group Policy Wizard where you can click on the ‘Finish” button.
All non-administrators. The Non-Administrators LGPO applies user policy settings to anyone who is not an administrator/included in a group of administrators. To do it, you need to press the Windows logo + R keys on your keyboard and then type MMC into the field and clicking on the OK button. Click Yes when prompted by User Account Control. Now in Microsoft Management Console, click on File, followed by Add/Remove snap-in from the menu. Choose the Local Group Policy Editor and click on the Add button. From the Select Group Policy Object window, click on the Browse button. Next, click on the Users tab and then choose the Non-Administrators group and click on the OK button. Lastly, click on the Finish button from the Group Policy Wizard screen.
Administrators. The Administrators LGPO applies policy settings to users who are members of the administrator’s group. To do it, you need to press the Windows logo + R keys on your keyboard and then type MMC into the field and clicking on the OK button. Click Yes when prompted by User Account Control. Now in Microsoft Management Console, click on File, followed by Add/Remove snap-in from the menu. Choose the Local Group Policy Editor and click on the Add button. From the Select Group Policy Object window, click on the Browse button. Next, click on the Users tab and then choose the Administrators group and click on the OK button. You’ll then be directed back to the Group Policy Wizard where you can click on the Finish button.
The Windows Defender is now turned off for as long as you don’t go back into the Local Group Policy Editor and change the checkmark to either Not Configured or Disabled. You’ll want to put it back on Not Configured just in case there is a feature available in future versions of Windows that allows you to start making changes to it from outside the Local Group Policy Editor. If you set it to Disable then the Windows Defender is always going to be turned on no matter what you want to do unless you make that change from within the Local Group Policy Editor.
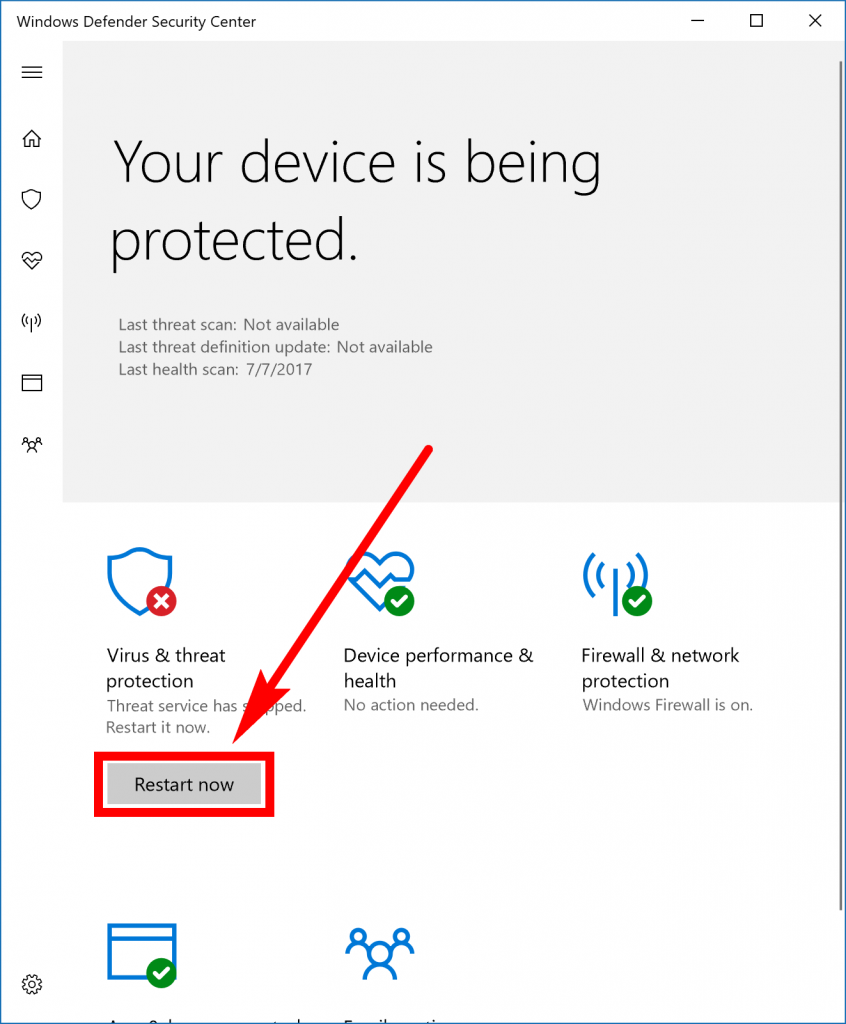
So, when you want to turn the Windows Defender anti-virus back on again, open the Local Group Policy Editor, follow the same path as you did above and change it from Enabled to Not Configured. Then type Windows Defender into your search field from the taskbar and click on the Windows Defender application under the Best match section. With Windows Defender open, click on the Restart Now button.
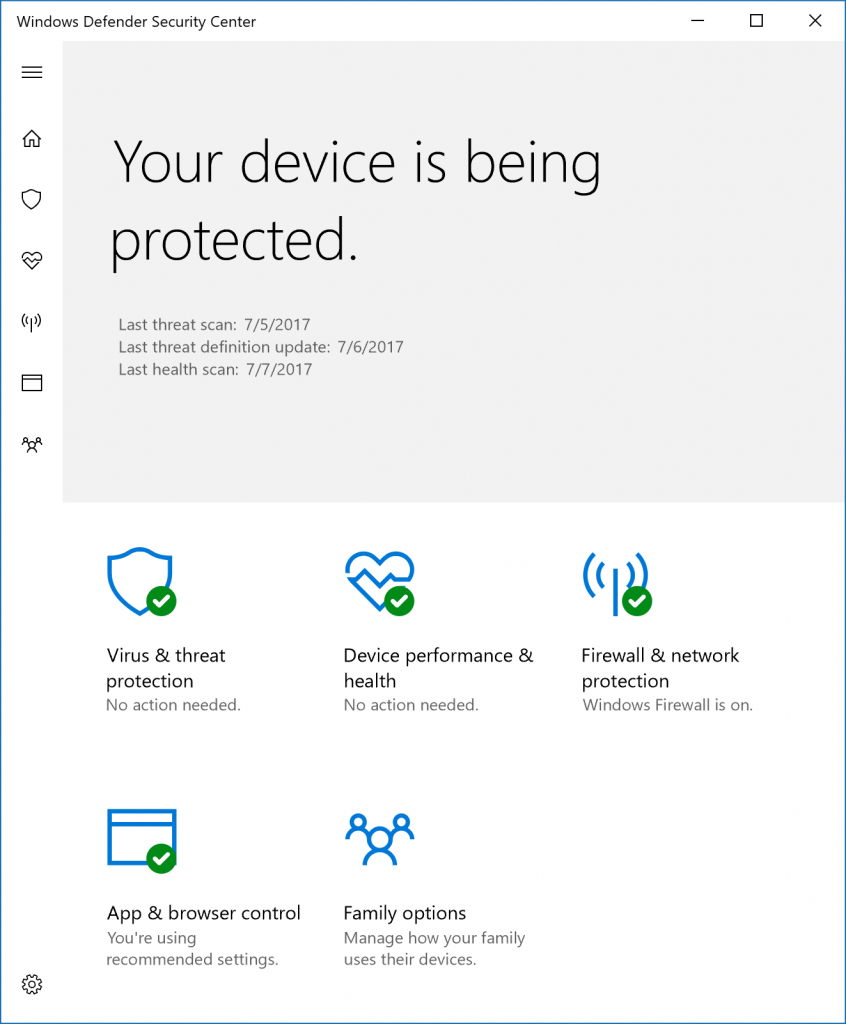
The Windows Defender program then starts running, and you can tell by the new green tick that is being shown where it has the Virus and Shield protection icon. It also says in big words above Your device is being protected.
You can now close the Windows Defender antivirus and be confident that your computer is being protected.
There are a lot of different opinions floating around out there about whether or not you should keep Windows Defender turned on or replace it with another anti-virus program from a third-party vendor that specializes in security. You could easily make a case for wanting to replace it because Microsoft has shown in the past that just because it is the billion dollar company, that doesn’t mean it bothers creating the best features for its operating system. There are lots of tools out there that are better for system images than what Microsoft is offering for backing up system images for itself. That said, if you want an opinion or insight in what I run, I think Windows Defender works just fine because I haven’t had any issues with it so far. I also continue to use it as my only anti-virus (you can only use one at a time.) Windows 10 also offers a separate anti-malware tool that is running scans in the background for you just like it does with Windows Defender. Both of those features packaged together is all the average user needs to stay secure. Relying on the scan results to make your decision isn’t a great way of going about it. It’s just as easy for Window Defender to act like it doesn’t see something as it is for something else like AVG to include additional items not worth worrying about in a scan report. What really matters is the results: how is your computer working and have you had any problems with it?
Related Tutorials